Dozens of risks threaten your business every day, and ignoring them will only make you more vulnerable. As remote work increases, it’s important to recognize the potential risks your employees create for your company. By understanding these insider threats, you can better prepare to educate your employees and protect your data through stronger security.
The Greatest Threat to Your Business
When picturing the biggest threat to your security, you might be tempted to think of a hacker in a foreign country or a virus being transmitted to your computer from miles away.
But in reality, one of the biggest threats to your security could be sitting in the cubicle next to your office.
Think about it.
Humans are unpredictable. They’re governed by emotions, personal traits, and ideologies that influence their day-to-day decisions.
And humans are also fallible.
According to Cybersecurity Intelligence, human error is the leading cause of security breaches, accounting for over 90% of cases.
What is an Insider Threat?
So how do you determine whether an employee poses a real threat?
An employee becomes an insider threat if they have some form of access to your IT systems and can use that access to harm your organization.
In general, there are 2 types of insider threats:
- Malicious
- Accidental
Malicious insiders are looking to harm your organization for personal gain. This includes committing fraud, stealing intellectual property, or sabotaging your infrastructure.
While accidental insiders aren’t intentionally trying to harm you, they can still be just as dangerous to your company. These insiders are generally fooled by attackers into handing over data or downloading malicious attachments. Phishing and man-in-the-middle attacks often lead to these kinds of security breaches.
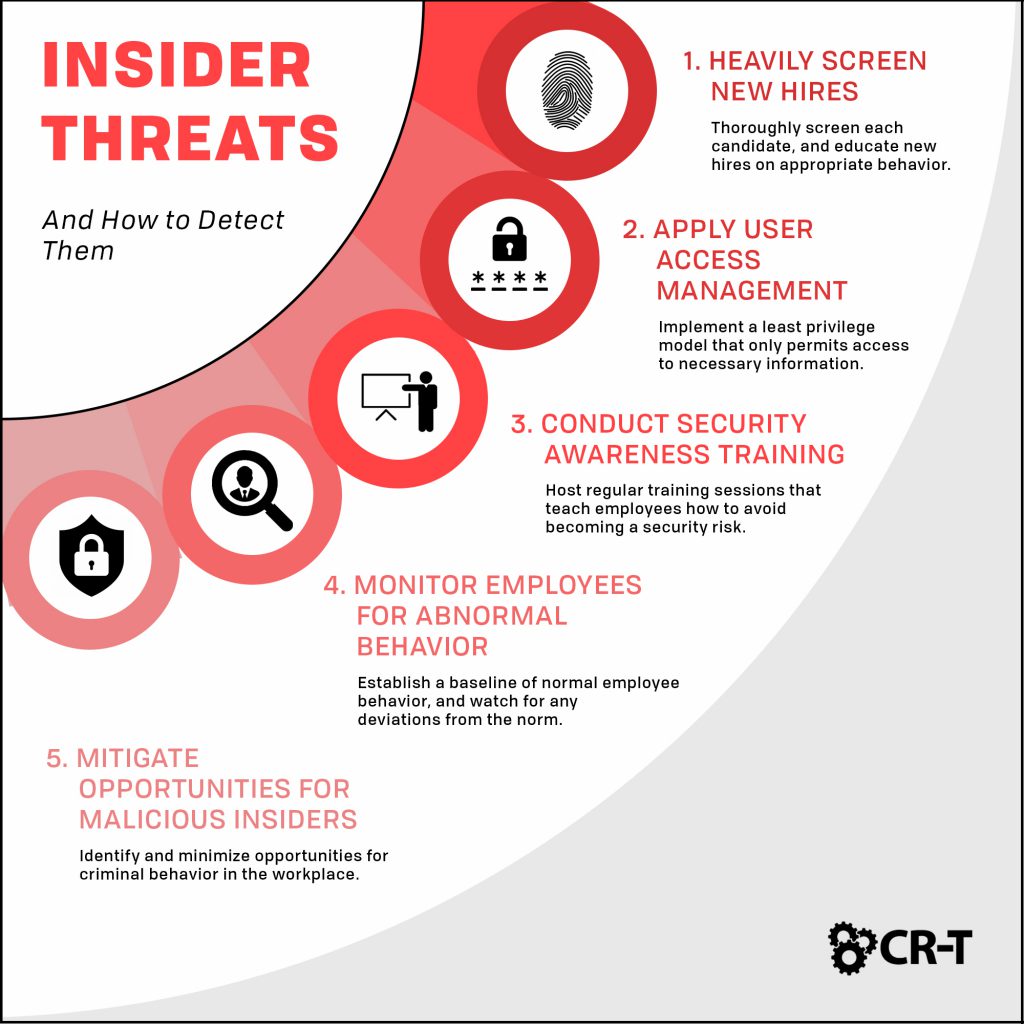
5 Best Practices for Insider Threat Detection
But even if you understand the danger of insider threats, detecting them is much harder.
Luckily, there are several best practices that will help you more easily detect insider threats and counteract them before they can cause harm to your business.
1. Heavily Screen New Hires
Detecting insider threats begins with your new and potential hires. Thoroughly screen each candidate through background checks and speaking with former employers/references.
When you hire a new employee, set clear expectations on what kind of behavior is deemed appropriate and what the consequences will be for any infractions. This will prevent potential misunderstandings in the future.
2. Apply User Access Management
User access management is critical for insider threat detection.
According to the Ponemon Institute, 62% of users report having access to company data that they shouldn’t see.
By limiting access to secure data, you reduce the chances of an employee stealing confidential information or otherwise jeopardizing the company.
The least privilege model ensures that employees only have access to information necessary to their job functions. This practice creates greater protection for your company and removes the temptation for employees to access unauthorized data.
3. Conduct Security Awareness Training
One of the best ways to prevent accidental insider threats is through employee training.
Host regular training sessions that teach employees how to avoid becoming a security risk. Your training might include topics like how to recognize phishing emails, the importance of secure remote access, and how to respond to a cyber attack.
At CR-T, we run phishing campaigns that help managers understand which kinds of attacks are most difficult for employees to recognize. That way, they can address these kinds of attacks during training meetings.
Encourage employees to flag emails that appear suspicious, and notify your IT team anytime something appears out of place on a company device or network. By learning how to recognize these threats early, your employees can become one of your greatest assets in preventing and responding to cyber attacks.
4. Monitor Employees for Abnormal Behavior
While training your employees will prevent most accidental insider threats, you still need to keep your eyes open.
Sometimes, you can detect insider threats before they become a larger problem by monitoring employee behavior.
- Start by establishing a baseline of normal behavior for each employee. What is their user access level? How many hours do they normally work? What kinds of files do they typically download?
- Once you have a solid measure of normal behavior, watch for deviations from the norm. Are any of your employees copying information unrelated to their jobs? Are they transferring unauthorized files or installing applications that haven’t been approved? Maybe they’re logging into your network at odd hours.
- Although this kind of behavior doesn’t immediately make your employee(s) a threat, it’s still important to follow up on any unusual activities. At the very least, you’ll find out that the employee has a specific reason for their behavior and that there’s nothing to worry about. But if something more suspicious is going on, you can stop the employee before their actions become a greater threat.
5. Mitigate Opportunities for Malicious Insiders
- The availability and ease of acquiring company property and/or information
- Improperly labeling classified information
- Undefined policies regarding remote work
- The perception of lax security or minimal consequences for theft
Finding an Insider Threat Solution
Insider threat management should be a priority at every company, but you shouldn’t have to handle the burden alone.
We provide IT security solutions that will strengthen your company’s policies and programs. Our team will help you find the gaps in your security so you feel better prepared to minimize insider threats and keep your organization protected.
Here at CR-T, we take pride in providing enterprise-level IT services at prices that work for small businesses. Our team of experts can become your IT support department, responding to issues quickly, often before you even know about them. Covering everything from your servers and network infrastructure to your computers, workstations and mobile devices, we provide end-to-end solutions for all your technology needs.
Time and experience have helped us develop best practices and workflow procedures designed to keep your focus on your business, not your technology.
Blog & Media
Cloud Services
Managed IT Support
Cyber Security
Project Services
Servers/Infrastructure
Firewalls
Networking
Hardware/Software
Microsoft Products/Cloud
Amazon Web Services
Penetration Testing vs Vulnerability Scanning
If you’re responsible for managing the security of your organization’s network or systems, you may have heard the terms “penetration testing” and “vulnerability testing” thrown
Backup and Disaster Recovery
Your organization can’t afford to neglect backup and disaster recovery. If it takes your business too long to get back online after a disaster, you
6 Steps to Secure Customer Data
Securing customer data is essential for one major reason: your business depends on it. As an IT director, you recognize the importance of cybersecurity when
5 Steps to Promote Compliance in the Workplace
You’re familiar with the ever-changing world of regulatory compliance. Robust compliance enables you to avoid legal liabilities while improving your organization’s effectiveness. And many of