Does your company have a cybersecurity policy? If so, when’s the last time you updated it?
Do you review your security procedures regularly? Or is your policy gathering dust somewhere on a shelf?
If you want your organization to prioritize security, then you need to keep your policies and practices relevant. By regularly reviewing and updating your cybersecurity policy, you can keep security at the forefront of your employees’ minds and better protect your data from outside threats.
Why Should You Have a Cybersecurity Policy?
But before you can worry about how often you should update your cybersecurity policy, you first need to have a policy in place.
Cybersecurity policies outline the rules for how your organization’s employees, partners, and customers can access and use your data. These policies generally follow a hierarchical structure, beginning with an overarching document that describes general security standards and expectations.
From there, a cybersecurity policy can extend further to identify key roles and responsibilities within the organization, outline preventative measures, and provide an extensive plan for responding to potential cyber attacks.
Without a cybersecurity policy, you’re leaving the fate of your organization—and its data—to chance.
According to new research from Gallagher, human error accounts for at least 60% of all cyber attacks.
And if your employees don’t have a solid understanding of cybersecurity best practices, then your business could end up as a statistic.
When Should You Review Your Cybersecurity Policies?
Unfortunately, once an organization establishes a cybersecurity policy, many executives tend to act as if these guidelines are set in stone and can never be changed. But this kind of thinking is dangerous.
Cyber threats are constantly evolving, and criminals regularly change their tactics and their targets.
By failing to stay up to date with these trends, you’re already setting yourself up for defeat.
But how and when should you update your cybersecurity policies?
We’ll start by sharing five indicators that it might be time to evaluate your cybersecurity policy.
In doing so, we’d like to point out that this isn’t a comprehensive list of all the times you should be revisiting your policy.
Your organization is unique, and it will be up to your executives to determine how often and how thorough each evaluation should be. This list is just here to get you started.
1. As Part of a Scheduled Evaluation
Regardless of the nature of your business, you should establish a regular schedule within your cybersecurity policy’s governance document. Whether this evaluation happens quarterly, semiannually, or annually, make sure a policy review is built into your corporate calendar.
By scheduling regular policy reviews, you’ll avoid the need to perform a major overhaul of your cybersecurity policy every few years. Instead, you can use these frequent review periods to evaluate the effectiveness of your policies and make small adjustments if necessary.
Whatever your timeline or frequency, the important thing is that you make policy evaluations a regular part of your business.
2. In Response to Regulatory Requirements
State, federal, and international laws and regulations change constantly to accommodate the ever-shifting climate of cybersecurity.
Your security and compliance teams need to be aware of any changes that could affect your organization’s cybersecurity platform.
Anytime there’s a regulatory change, your organization should host a policy review to determine the impact of these regulations and make any necessary changes to your cybersecurity policy. Keep in mind how long these changes will take to implement and how they might affect other business operations.
Don’t wait for an audit or the date of your next scheduled policy review. By immediately investigating the impact of the change and adapting your policies, you can support a smoother transition for your organization when the new law takes effect.
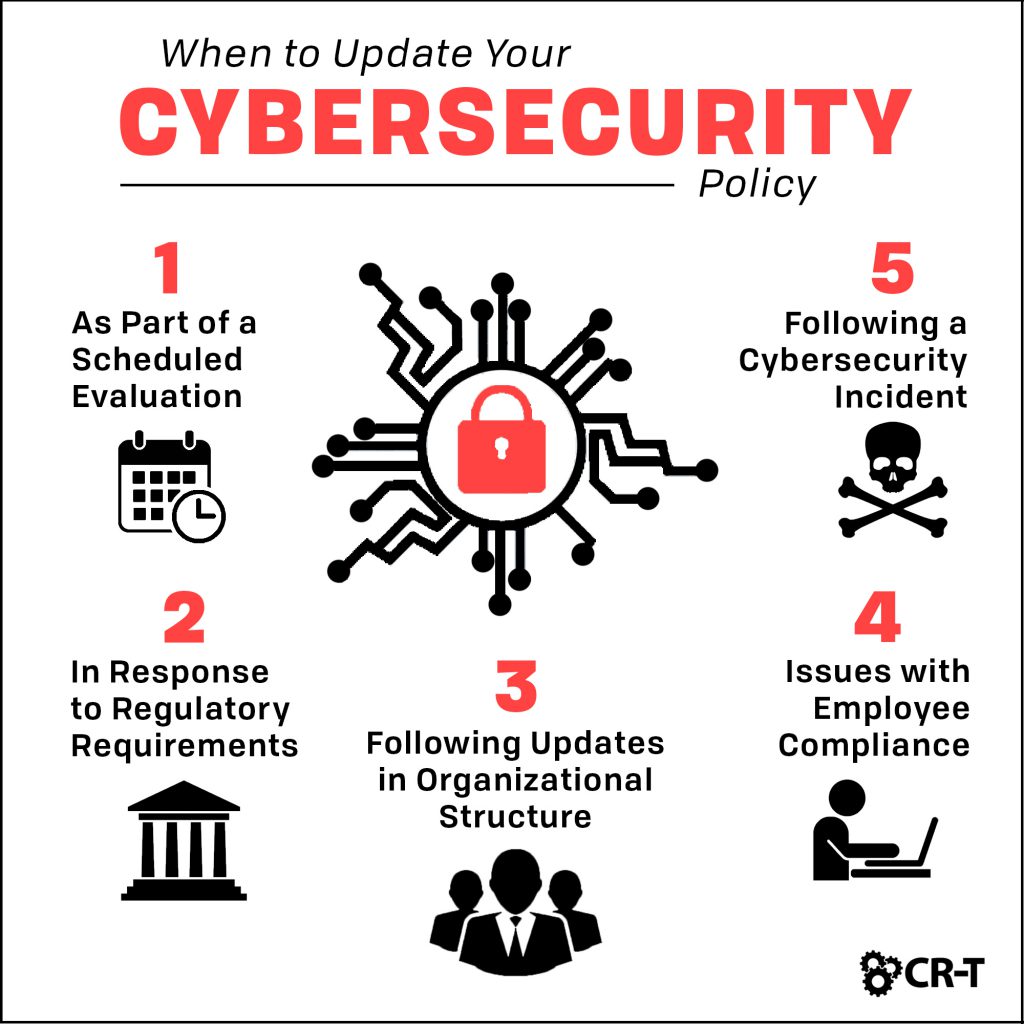
3. Following Updates in Organizational Structure
- New branches or offices open.
- New applications, devices, or services are added to your network.
- Any of your systems are retired or decommissioned.
- Changes are made to employee work operations. (ie: instituting a “Bring Your Own Device” (BYOD) policy, changing core work hours, giving employees the option to work remotely, etc.)
- Any of your services or operations are outsourced.
4. When There are Issues with Employee Compliance and Adoption
- Are your organization’s cybersecurity policy objectives, goals, and standards clear?
- Are security procedures difficult to follow?
- Have new technologies or processes been introduced that aren’t addressed in the current policy?
- Are employees receiving adequate training on cybersecurity awareness?
- Do employees and managers have any suggestions on how to improve these policies or the adoption of cybersecurity practices?
5. Following a Cybersecurity Threat or Incident
You should never wait until an incident occurs before reviewing your cybersecurity policy.
However, these threats can serve as a way to strengthen your policies and avoid future attacks.
Immediately after the damage of the incident is contained and your operations have been recovered, security and management teams should conduct a debriefing of the incident.
Discuss what caused the incident, what the consequences were, and whether the existing policies were effective. This debriefing could include interviewing employees and examining system and security tool logs.
From there, management can decide whether changes in security procedures need to be made and whether employee training can be updated to enhance understanding of these policies.
However, if the event is an isolated incident and the existing policies are deemed sufficient, then no changes need to be made.
Keep Your Security Strong and Your Data Safe
With the number of cyber attacks increasing every year, you can’t be too prepared when it comes to your cybersecurity.
Regularly reviewing and updating your cybersecurity policy is one of the most effective ways to make sure your employees are on the same page and your security is up to date.
If you aren’t sure how to get started, our team help you identify your current level of security and create a plan that’s customized for your business.
Schedule a free consultation today!
Here at CR-T, we take pride in providing enterprise-level IT services at prices that work for small businesses. Our team of experts can become your IT support department, responding to issues quickly, often before you even know about them. Covering everything from your servers and network infrastructure to your computers, workstations and mobile devices, we provide end-to-end solutions for all your technology needs.
Time and experience have helped us develop best practices and workflow procedures designed to keep your focus on your business, not your technology.
Blog & Media
Cloud Services
Managed IT Support
Cyber Security
Project Services
Servers/Infrastructure
Firewalls
Networking
Hardware/Software
Microsoft Products/Cloud
Amazon Web Services
Penetration Testing vs Vulnerability Scanning
If you’re responsible for managing the security of your organization’s network or systems, you may have heard the terms “penetration testing” and “vulnerability testing” thrown
Backup and Disaster Recovery
Your organization can’t afford to neglect backup and disaster recovery. If it takes your business too long to get back online after a disaster, you
6 Steps to Secure Customer Data
Securing customer data is essential for one major reason: your business depends on it. As an IT director, you recognize the importance of cybersecurity when
5 Steps to Promote Compliance in the Workplace
You’re familiar with the ever-changing world of regulatory compliance. Robust compliance enables you to avoid legal liabilities while improving your organization’s effectiveness. And many of